Professor Rybolov’s Guide to InfoSec and Public Policy Analysis
Posted May 17th, 2010 by rybolovHaving just finished our mini-semester class on InfoSec and Public Policy, I want to share with my old friend, the Interweblagosphere, a small process/framework for doing some analysis. This can be a paper, legislation, or even a basic guideline for developing metrics.
- Problemspace Definition: Give a point-of-view on a particular subject and why it is important. Thinking more conventionally, what is it exactly that is your thesis statement?
- History of Incident: prove the problem is worth time to solve. Usually this involves identifying a handful of large-scale incidents that can serve as the model for your analysis. Looking at these incidents, what worked and what didn’t work? Start to form some opinions. You will revisit these incidents later on as models.
- Regulatory Bodies: beginning of stakeholder definition. Identify responsible Government or industry-specific organizations and their history of dealing with the problem. What existing strategic plans and reports exist that you can use to feed your analysis.
- Private Sector Support: more stakeholders. How much responsibility does private industry have in this issue and what is the impact on them? They can be owners (critical infrastructure), vendors (hardware, software, firmware), maintainers, etc.
- Other Stakeholders: Consider end users, people who depend on the service that depends on the IT and the information therein.
- Trend and Metrics: what do we know about the topic given published metrics or our analysis of themes across our key incidents? If you notice a lack of metrics on the subject, what would be your “wish list” and what plan do you have for getting these metrics? For information security, this typically a huge gap–either we’re creating metrics to show where we’ve succeeded at the tactical level or we’re generating metrics with surveys which are notoriously flawed.
- Options and Alternatives Analysis: pros and cons, what evidence suggests each might succeed. Take your model incidents and run your options through them, would they help with each scenario? Gather up more incidents and see how the options would affect them. As you run through each option and scenario, consider each of the following:
- Efficacy of the Option–does it actually solve the root cause of the problem?
- Winner Stakeholders
- Loser Stakeholders
- Audit Burden
- Direct Costs
- Indirect Costs
- Build Strategic Plan and Recommendations: Based on your analysis of the situation (model incidents, metrics, and power dynamics), build recommendations from the high-performing options and form them into a strategic plan. The more specific you can get, the better.
Note that for the most part these are not exclusive to information security but to public policy analysis in general. There are a couple parts that need emphasis because of the immature nature of infosec.
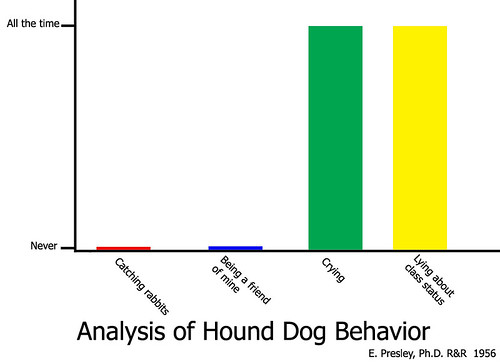
Analysis of Hound Dog Behavior graph by MShades. Our analysis is a little bit more in-depth. =)
Then the criteria for evaluating the strategic plan and the analysis leading up to it:
- Has an opinion
- Backs up the opinion by using facts
- Has models that are used to test the options
- Lays out a well-defined plan
As usual, I stand on the shoulders of giants, in this case my Favorite Govie provided quite a bit of input in the form of our joint syllabus.
Similar Posts:
Posted in Public Policy, What Works |  2 Comments »
2 Comments »
Tags: infosharing • legislation • publicpolicy • security
 Posts RSS
Posts RSS

May 17th, 2010 at 11:03 am
[…] This post was mentioned on Twitter by grecs, novainfosec. novainfosec said: #NOVABLOGGER: Professor Rybolov’s Guide to InfoSec and Public Policy Analysis http://bit.ly/cGQILr http://j.mp/nispblog […]
May 21st, 2010 at 2:05 pm
[…] know where to start? Rybolov shares his guide to infosec and public policy analysis with us. Click here to learn from the professor […]