I’ve seen the scenario about a dozen times in the last 2 months–contractors and service providers of all sorts responding to the Government’s security requirements in the middle of a contract. It’s almost reached the stage where I have it programmed as a “battle drill” ala the infantryman’s Battle Drill 1A, and I’m here to share the secret of negotiating these things.
Let’s see, without naming names, let’s look at where I’ve seen this come up:
- Non-Government Organizations that assist the Government with para-Government services to the citizens
- Companies doing research and development funded by the Government–health care and military
- Universities who do joint research with the Government
- Anybody who runs something that the Government has designated as “critical infrastructure”
- State and local governments who use Federal Government data for their social plans (unemployment system, food stamps, and ) and homeland security-esque activities (law enforcement, disaster response)
- Health Care Providers who service Government insurance plans
For the purposes of this blog post, I’ll refer to all of these groups as contractors or service providers. Yes, I’m mixing analogies, making huge generalizations, and I’m not precise at all. However, these groups should all have the same goals and the approach is the same, so bear with me while I lump them all together.
Really, guys, you need to understand both sides of the story because this a cause for negotiations. I’ll explain why in a minute.
On the Government side: Well, we have some people we share data with. It’s not a lot, and it’s sanitized so the value of it is minimal except for the Washington Post Front Page Metric. Even so, the data is PII that we’ve taken an anonymizer to so that it’s just statistical data that doesn’t directly identify anybody. We’ve got a pretty good handle on our own IT systems over the past 2 years, so our CISO and IG want us to focus on data that goes outside of our boundaries. Now I don’t expect/want to “own” the contractor’s IT systems because they provide us a service, not an IT system. My core problem is that I’m trying to take an existing contract and add security requirements retroactively to it and I’m not sure exactly how to do that.
Our Goals:
- Accomplishing the goals of the program that we provided data to support
- Protection of the data outside of our boundaries
- Proving due-diligence to our 5 layers of oversight that we are doing the best we can to protect the data
- Translating what we need into something the contractor understands
- Being able to provide for the security of Government-owned data at little to no additional cost to the program
On the contractor/service provider side: We took some data from the Government and now they’re coming out of the blue saying that we need to be FISMA-compliant. Now I don’t want to sound whiney, but this FISMA thing is a huge undertaking and I’ve heard that for a small business such as ourselves, it can cripple us financially. While I still want to help the Government add security to our project, I need to at least break even on the security support. Our core problem is to keep security from impacting our project’s profitability.
Our Goals:
- Accomplishing the goals of the program that we were provided data to support
- Protection of the data given to us to keep the Government happy and continuing to fund us (the spice must flow!)
- Giving something to the Government so that they can demonstrate due-diligence to their auditors and IG
- Translating what we do into something the Government understands
- Keeping the cost of security to an absolute minimum or at least funded for what we do add because it wasn’t scoped into the SOW
Hmm, looks like these goals are very much in alignment with each other. About the only thing we need to figure out is scope and cost, which sounds very much like a negotiation.

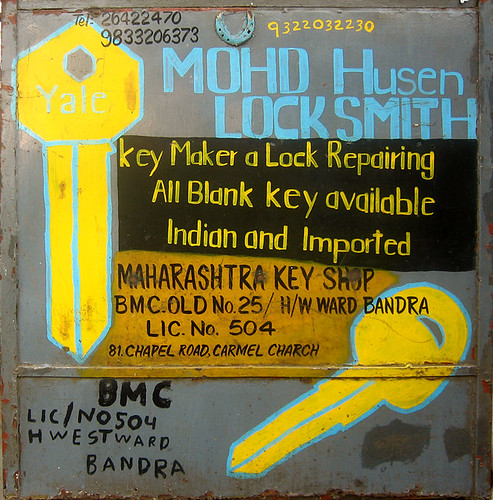
Hardcore Negotiation Skills photo by shinosan.
Little-known facts that might help in our scenario here:
- Section 2.4 of SP 800-53 discusses the use of compensating controls for contractor and service-provider systems.
- One of the concepts in security and the Government is that agencies are to provide “adequate security” for their information and information systems. Have a look at FISMA and OMB Circular A-130.
- Repeat after me: “The endstate is to provide a level of protection for the data equivalent or superior to what the Government would provide for that data.”
- Appendix G in SP 800-53 has a traceability matrix through different standards that can serve as a “Rosetta Stone” for understanding each other. Note to NIST: let’s throw in PCI-DSS, Sarbanes-Oxley, and change ISO 17799 to 27001.
So what’s a security geek to do? Well, this, dear readers, is Rybolov’s 5-fold path to Government/contractor nirvana:
- Contractor and Government have a kickoff session to meet each other and build raport, starting from a common ground such as how you both have similar goals. The problem really is one of managing each others’ expectations.
- Both Government and Contractor perform internal risk assessment to determine what kind of outcome they want to negotiate.
- Contractor and Government meet a week later to negotiate on security.
- Contractor provides documentation on what security controls they have in place. This might be as minimal as a contract with the guard force company at their major sites, or it might be just employee background checks and
- Contractor and Government negotiate for a 6-month plan-of-action. For most organizations considering ISO 27001, this is a good time to make a promise to get it done. For smaller organizations or data , we may not even
Assumptions and dependencies:
- The data we’re talking about is low-criticality or even moderate-criticality.
- This isn’t an outsourced IT system that could be considered government-owned, contractor-operated (GO-CO)
Similar Posts:
 No Comments »
No Comments » Posts RSS
Posts RSS