Posted December 12th, 2011 by
rybolov
Contrary to what you might hear this week in the trade press, FedRAMP is not fully unveiled although there was some much-awaited progress. There was a memo that came out from the administration (PDF caveat). Basically what it does is lay down the authority and responsibility for the Program Management Office and set some timelines. This is good, and we needed it a year and a half ago.
However, people need to stop talking about how FedRAMP has solved all their problems because the entire program isn’t here yet. Until you have a process document and a catalog of controls to evaluate, you don’t know how the program is going to help or hinder you, so all the press about it is speculation.
Similar Posts:
Posted in DISA, FISMA, NIST, Outsourcing, Risk Management |  No Comments »
No Comments »
Tags: 800-37 • 800-53 • 800-53A • accreditation • C&A • catalogofcontrols • categorization • certification • cloud • cloudcomputing • comments • compliance • dhs • fedramp • fisma • government • infosec • infosharing • itsatrap • management • moneymoneymoney • NIST • omb • scalability • security
Posted November 21st, 2011 by
rybolov
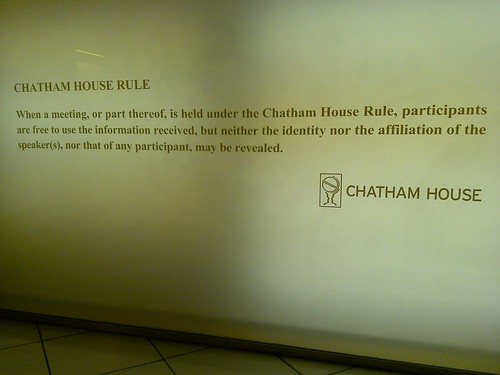
So while I was at some conferences over the past couple of months, I had an awesome idea while sitting in a panel about data breaches, especially notification. While streaming conferences is pretty awesome for most content, I keep thinking that we need that as an industry we need the exact opposite: a track of the conference that is completely off-the-record.
Here in DC when we do smaller training sessions, we invoke the Chatham House Rule. That is, the discussion is for non-attribution. There are several reasons behind this:
- You don’t have to worry (too much, anyway) about vendors in attendance selling you something
- It won’t end up in the press
- It gets real information to people instead of things that are “fit for public consumption”
My local area has a hackers association (No linkie, if you have minimal skill you can find it) that meets to talk about mostly technical stuff and what folks are working on. I find that more and more often when I do a talk there I do it “Off the Record” for a wide variety of reasons:
- I don’t want the attackers to get more effective
- I have half-baked ideas where I want/need feedback on if they are completely off-base
- The subject matter is in a legal gray-area and I’m not a lawyer
- I talk “on the record” all day every day about the same things
- I can “test-drive” presentation material to see how it works
- I can show nuts and bolts
So, the point of all this is that maybe we need to start having more frank discussions about what the bad guys are doing “in the wild” if we want to stop them, and that involves talking with peers from other companies inside the same industry to see what they are getting hit with.
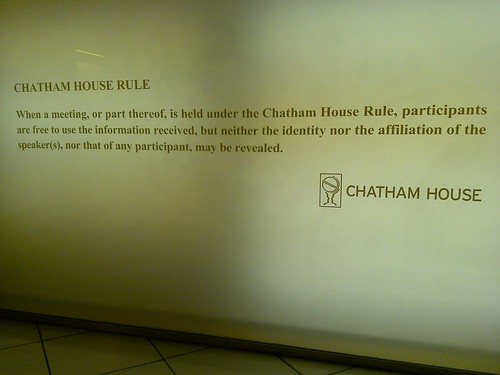
Chatham House Rule photo by markhillary.
Similar Posts:
Posted in Public Policy, Speaking, What Doesn't Work, What Works |  No Comments »
No Comments »
Tags: government • infosec • infosharing • security • speaking
Posted November 4th, 2011 by
rybolov
Job announcement is here. Share with anybody you think can do it.
Similar Posts:
Posted in FISMA, NIST, Odds-n-Sods |  1 Comment »
1 Comment »
Tags: compliance • government • infosec • itsatrap • job • NIST • risk • security
Posted September 23rd, 2011 by
rybolov
Ah yes, you now know how I spend my Saturday mornings lately.

Similar Posts:
Posted in DDoS, IKANHAZFIZMA |  No Comments »
No Comments »
Tags: ddos • denial of service • dos • infosec • lolcats • pwnage • scalability • security
Posted September 23rd, 2011 by
rybolov
Let me tell you a little story.
So September 17th was Constitution Day and was celebrated by protestors in most major cities across the US with a sizable percentage of folks on Wall Street in NYC. In conjunction with this protest, a new Denial-of-Service tool, #RefRef, was supposed to be released. It supposedly used some SQL Injection techniques to put a file (originally listed as a JavaScript but Java is more believable) on application or database servers that then created massive amounts of OS load, thereby crippling the server. The press coverage of the tool does have the quote of the year: ““Imagine giving a large beast a simple carrot, [and then] watching the best choke itself to death.” Seriously?
Then came the 17th. I checked the site, whoa, there is some perl code there. Then I read it and it sounded nothing like the tool as described. Rumor around the Intertubes was that #RefRef was/is a hoax and that the people responsible were collecting donations for R&D.
This is what we actually have for the tool that was released on the RefRef site does:
GET /%20and%20(select+benchmark(99999999999,0x70726f62616e646f70726f62616e646f70726f62616e646f)) HTTP/1.1
TE: deflate,gzip;q=0.3
Connection: TE, close
Host: localhost
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; nl; rv:1.8.1.12) Gecko/20080201Firefox/2.0.0.12
The way this works is that it requests a large amount of benchmark queries against the database. This is very similar to SQL Injection in that the request contains database commands which are then passed by the application server to the database. In this case, the SQL command is “benchmark” which executes the query multiple times to build test performance of the query. As you would guess, it generates a ton of database server load. However, it’s only applicable to MySQL.
Similar Posts:
Posted in DDoS, Technical |  No Comments »
No Comments »
Tags: ddos • dos • infosec • pwnage • scalability
Posted September 2nd, 2011 by
rybolov
Here at IKANHAZFIZMA, we’re training the next generation of Apache webserver Denial-of-Service gurus. It involves punching bags, some nomz for the troops, and lots of requests for kibble.

Similar Posts:
Posted in DDoS, IKANHAZFIZMA |  No Comments »
No Comments »
Tags: ddos • infosec • lolcats • pwnage • security
 No Comments »
No Comments » Posts RSS
Posts RSS