Posted April 1st, 2010 by
rybolov
Well, several funny things happened, they happen every week. But specifically I’m talking about the hearing in the House Committee on Homeland Security on FISMA reform–Federal Information Security: Current Challenges and Future Policy Considerations. If you’re in information security and Government, you need to go read through the prepared statements and even watch the hearing.
Also referenced is HR.4900 which was introduced by Representative Watson as a modification to FISMA. I also recommend that you have a look at it.
Now for my comments and rebuttals to the testimony:
- On the cost per sheet of FISMA compliance paper: If you buy into the State Department’s cost of $1700 per sheet, you’re absolutely daft. The cost of a security program divided by the total number of sheets of paper is probably right. In fact, if you do the security bits right, your cost per sheet will go up considerably because you’re doing much more security work while the volume of paperwork is reduced.
- Allocating budget for red teams: Do we really need penetration testing to prove that we have problems? In Mike Smith’s world, we’re just not there yet, and proving that we’re not there is just an excuse to throw the InfoSec practitioners under the bus when they’re not the people who created the situation in the first place.
- Gus Guissanie: This guy is awesome and knows his stuff. No, really, the guy is sharp.
- State Department Scanning: Hey, it almost seems like NIST has this in 800-53. Oh wait, they do, only it’s given the same precedence as everything else. More on this later.
- Technical Continuous Monitoring Tools: Does anybody else think that using products of FISMA (SCAP, CVE, CVSS) as evidence that FISMA is failing is a bit like dividing by zero? We really have to be careful of this or we’ll destroy the universe.
- Number of Detected Attacks and Incidents as a Metric: Um, this always gets a “WTF?” from me. Is the number increasing because we’re monitoring better or is it because we’re counting a whole bunch of small events as an attack (ie, IDS flagged on something), or is it because the amount of attacks are really increasing? I asked this almost 2 years ago and nobody has answered it yet.
- The Limitations of GAO: GAO are just auditors. Really, they depend on the agencies to not misrepresent facts and to give them an understanding of how their environment works. Auditing and independent assessment is not the answer here because it’s not a fraud problem, it’s a resources and workforce development problem.
- OMB Metrics: I hardly ever talk bad about OMB, but their metrics suck. Can you guys give me a call and I’ll give you some pointers? Or rather, check out what I’ve already said about federated patch and vulnerability management then give me a call.
So now for Rybolov’s plan to fix FISMA:
- You have to start with workforce management. This has been addressed numerous times and has a couple of different manifestations: DoDI 8570.10, contract clauses for levels of experience, role-based training, etc. Until you have an adequate supply of clueful people to match the demand, you will continue to get subpar performance.
- More testing will not help, it’s about execution. In the current culture, we believe that the more testing we do, the more likely the people being tested will be able to execute. This is highly wrong and I’ve commented on it before. I think that if it was really a fact of people being lazy or fraudulent then we would have fixed it by now. My theory is that the problem is that we have too many wonks who know the law but not the tech and not enough techs that know the law. In order to do the job, you need both. This is also where I deviate from the SANS/20 Critical Security Controls approach and the IGs that love it.
- Fix Plans of Actions and Milestones. These are supposed to be long-term/strategic problems, not the short-term/tactical application of patches–the tactical stuff should be automated. The reasoning is that you use these plans for budget requests for the following years.
- Fix the budget train. Right now the people with the budget (programs) are not the people running the IT and the security of it (CIO/CISO). I don’t know if the answer here is a larger dedicated budget for CISO’s staff or a larger “CISO Tax” on all program budgets. I could really policy-geek out on you here, just take my word for it that the people with the money are not the people protecting information and until you account for that, you will always have a problem.

Sights Around Capital Hill: Twice Sold Tales photo by brewbooks. Somehow seems fitting, I’ll let you figure out if there’s a connection. =)
Similar Posts:
Posted in FISMA, Public Policy, Rants, Risk Management |  7 Comments »
7 Comments »
Tags: accreditation • auditor • C&A • catalogofcontrols • certification • comments • compliance • fisma • gao • government • infosec • law • legislation • management • metrics • NIST • omb • publicpolicy • scalability • scap • security
Posted December 1st, 2009 by
rybolov
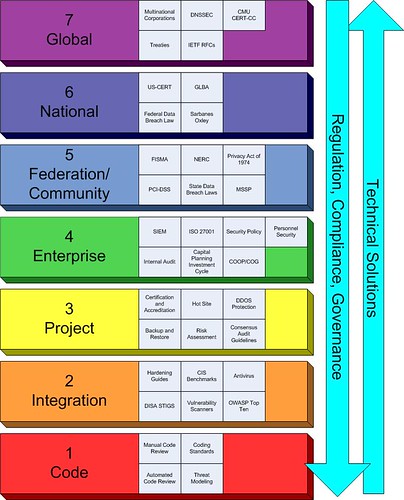
OK, so it’s been a couple of months of thinking about this thing. I threw together a rainbow-looking beast that now occupies my spare brain cycles.
Rybolov’s Information Security Management Model
And some peculiarities of the model that I’ve noticed:
Regulation, Compliance, and Governance flows from the top to the bottom. Technical solutions flow from the bottom to the top.
The Enterprise (Layer 4) gets the squeeze. But you CISOs out there knew that already, right? It makes much sense in the typical information security world to focus on layers 3, 4, and 5 because you don’t usually own the top and the bottom of the management stack.
The security game is changing because of legislation at layers 5 and 6. Think national data breach law. It seems like the trend lately is to throw legislation at the problems with information security. The scary part to me is that they’re trying to take concepts that work at layers 3 and 4 and scale them up the model with very mixed results because there isn’t anybody doing studies at what happens above the Enterprise. Seriously here, we’re making legislation based on analogies.
Typically each layer only knows about the layer above and below it. This is a serious problem when you have people at layers 5 and 6 trying to create solutions that carry down to layers 1 through 4.
At layers 1 and 2, you have the greatest chance to solve the root causes of security problems. The big question here is “How do we get the people working at these layers the support that they need?”
Similar Posts:
Posted in Public Policy |  7 Comments »
7 Comments »
Tags: government • infosec • legislation • management • publicpolicy • scalability • security
Posted October 16th, 2009 by
rybolov
My presentation slides from Sector 2009. This was a really fun conference, the Ontario people are really, really nice.
Presentation Abstract:
The US Federal Government is the world’s largest consumer of IT products and, by extension, one of the largest consumers of IT security products and services. This talk covers some of the problems with security on such a massive scale; how and why some technical, operational, and managerial solutions are working or not working; and how these lessons can be applied to smaller-scale security environments.
Similar Posts:
Posted in FISMA, NIST, Public Policy, Speaking, The Guerilla CISO, What Works |  No Comments »
No Comments »
Tags: catalogofcontrols • certification • compliance • fisma • government • infosec • infosharing • law • legislation • management • publicpolicy • scalability • scap • security • speaking
Posted August 24th, 2009 by
rybolov
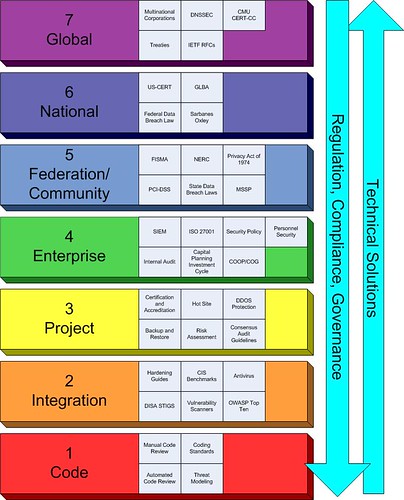
So we all know the OSI model by heart, right? Well, I’m offering up my model of technology management. Really at this stage I’m looking for feedback
- Layer 7: Global Layer. This layer is regulated by treaties with other nation-states or international standards. I fit cybercrime treaties in here along with the RFCs that make the Internet work. Problem is that security hasn’t really reached much to this level unless you want to consider multinational vendors and top-level cert coordination centers like CERT-CC.
- Layer 6: National-Level Layer. This layer is an aggregation of Federations and industries and primarily consists of Federal law and everything lumped into a “critical infrastructure” bucket. Most US Federal laws fit into this layer.
- Layer 5: Federation/Community Layer. What I’m talking here with this layer is an industry federated or formed in some sort of community. Think major verticals such as energy supply. It’s not a coincidence that this layer lines up with DHS’s critical infrastructure and key resources breakdown but it can also refer to self-regulated industries such as the function of PCI-DSS or NERC.
- Layer 4: Enterprise Layer. Most security thought, products, and tools are focused on this layer and the layers below. This is the realm of the CSO and CISO and roughly equates to a large corporation.
- Layer 3: Project Layer. Collecting disparate technologies and data into a similar piece such as the LAN/WAN, a web application project, etc. In the Government world, this is the location for the Information System Security Officer (ISSO) or the System Security Engineer (SSE).
- Layer 2: Integration Layer. Hardware, software, and firmware combine to become products and solutions and is focused primarily on engineering.
- Layer 1: Code Layer. Down into the code that makes everything work. This is where the application security people live.
There are tons of way to use the model.I’m thinking each layer has a set of characteristics like the following:
- Scope
- Level of centralization
- Responsiveness
- Domain expertise
- Authority
- Timeliness
- Stakeholders
- Regulatory bodies
- Many more that I haven’t thought about yet

Chocolate Layer Cake photo by foooooey.
My whole point for this model is that I’m going to try to use it to describe the levels at which a particular problem resides at and to stimulate discussion on what is the appropriate level at which to solve it. For instance, take a technology and you can trace it up and down the stack. Say Security Event and Incident Monitoring:
- Layer 7: Global Layer. Coordination between national-level CERTs in stopping malware and hacking attacks.
- Layer 6: National-Level Layer. Attack data from Layer 5 is aggregated and correlated to respond to large incidents on the scale of Cyberwar.
- Layer 5: Federation/Community Layer. Events are filtered from Layer 4 and only the confirmed events or interest are correlated to determine trends.
- Layer 4: Enterprise Layer. Events are aggregated by a SIEM with events of interest flagged for response.
- Layer 3: Project Layer. Logs are analyzed in some manner. This is most likely the highest in the model that we
- Layer 2: Integration Layer. Event logs have to be written to disk and stored for a period of time.
- Layer 1: Code Layer. Code has to be programmed to create event logs.
I do have an ulterior motive. I created this model because most of our security thought, doctrine, tools, products, and solutions work at Layer 4 and below. What we need is discussion on Layers 5 and above because when we try to create massively-scaled security solutions, we start to run into a drought of information at what to do above the Enterprise. There are other bits of doctrine that I want to bring up, like trying to solve any problem at the lowest level for which it makes sense. So in other words, we can use the model to propose changes to the way we manage security… say we have a problem like the lack of data on data breaches. What we’re saying when we say that we need a Federal data breach law is that because of the scope and the amount of responsibility and competing interests at Layer 5, that we need a solution at Layer 6, but in any case we should start at the bottom and work our way up the model until we find an adequate scope and scale.
So, this is my question to you, Internet: have I just reinvented enterprise public policy, IT architecture (Federal Enterprise Architecture) and business blueprinting, or did I create some kind of derivative view of technology, security, and public policy that I can now use?
Similar Posts:
Posted in Public Policy |  6 Comments »
6 Comments »
Tags: categorization • compliance • Cyberwar • dhs • fisma • government • infosec • infosharing • law • legislation • management • publicpolicy • scalability • security
Posted August 4th, 2009 by
rybolov
So let me give you a hypothetical job:
- You have to give up your high-paying private-sector job to be a Government employee
- You have tons of responsibility
- You have no real authority
- You have no dedicated budget
- You have no staffers
- The job has had half a dozen people filling it in the last 7 years
- The job has been open longer than it’s been staffed over the past 7 years
And yet this is what we’re asking candidates to do in order to even be a candidate for the Cybersecurity Coordinator. Yes, this is the exact same problem that all CISOs have with having a huge helping of responsibility and none of the authority to get things done, only we scaled it up and out to a national-level CISO position.
Somebody’s even gone as far to say that the lack of candidates for the job is the security field’s way of sending the message that you didn’t scope the job right. I think this opinion has much merit. CISOs being what they are, they’re usually pretty astute at walking into an ambush, and this job has all the makings of a good one.
I’ll even turn it around the other way and say that the security industry has yet to produce a CISO’s CISO–somebody who can do politics, budget, security, IT, and consensus-building all in one person. We have lots of people who can manage the enterprise and below, but it’s that additional little bit of political intrigue that is what we’re missing. Security people usually avoid politics like the bubonic plague because we’re an industry full of people who say it like it really is. This is a detriment in sales and politics.
So in true Guerilla-CISO fashion of not pointing out problems without offering something as a fix (no matter how much of a strawman arguement it really is), this is what we need to do to get people interested in being the Cybersecurity Czar^wCoordinator:
- A really well-defined scope. One person cannot do everything that we are asking for at this price (or any price for that matter).
- A budget for an operating staff where the number is more than than 8 digits.
- Statutory authority over the various departments and agencies responsible for cybersecurity: NCSD, S&T, DoJ, FBI, Commerce. Indirect influence doesn’t work here, never has.
- The direct ear of the President. Councils are OK, but puhlease, you want to get the job done, this is what it will take.
Then I read back through my list and realized that we really do need a law to create the Cybersecurity Czar position with everything that I just mentioned. But here’s the rub: legislation is slow, the bills to make the Cybersecurity Czar aren’t even going to be looked at until the next congressional session because we’re still trying to figure out the budget for last year.
I also think that what we’re calling the Cybersecurity Czar is really 2 jobs. You need somebody working for the Government CIO Vivek Kundra as the executive-branch CISO and you need a more senior person who worries about the military-industrial base, the critical infrastructure, the support to American commerce, and the protection of little old grandmas who represent the end-users.

Tsar’s Cannon photo by Siyad Ma. Now that’s some teeth for the position.
Similar Posts:
Posted in Cyberwar, Public Policy, Rants, What Doesn't Work |  1 Comment »
1 Comment »
Tags: Cyberwar • infosec • itsatrap • law • legislation • management • security

 7 Comments »
7 Comments » Posts RSS
Posts RSS